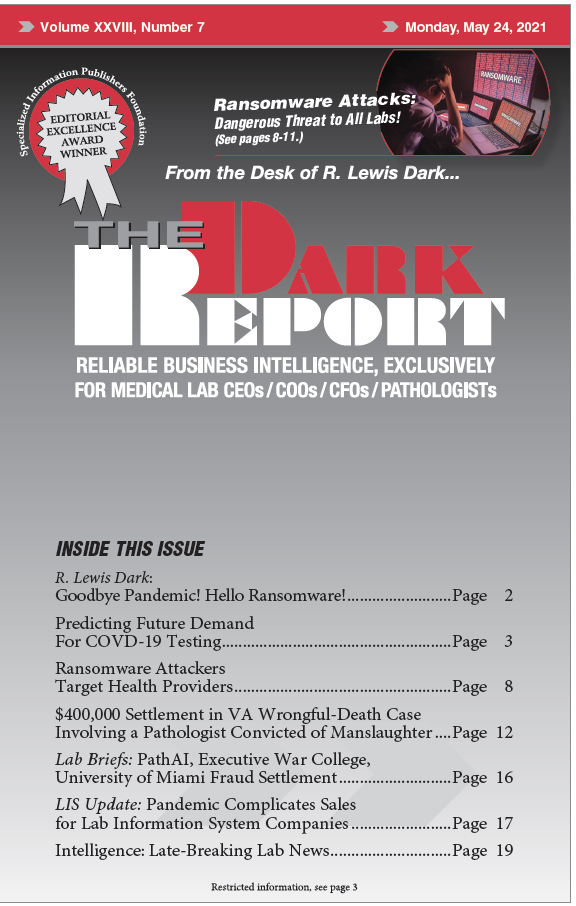
CEO SUMMARY: Both malware and ransomware have been around for a number of years. But the attacks launched today against healthcare providers are more sophisticated and better at achieving the total shutdown of targeted hospitals, doctor groups, and clinical laboratories. For this reason, clinical labs and pathology groups should put ransomware high on their list …
Ransomware Attackers Target Health Providers Read More »
To access this post, you must purchase The Dark Report.