CEO SUMMARY: Lab managers should take steps to protect patient data and proprietary information. This includes customer lists, payer contracts, customer-specific pricing, sales force compensation information, lab testing intellectual property, and protected health information. Technology now makes it easy for a departing employee to collect company data by moving it to a USB drive or …
Actions of Ex-Employees Can Breach Lab Security Read More »
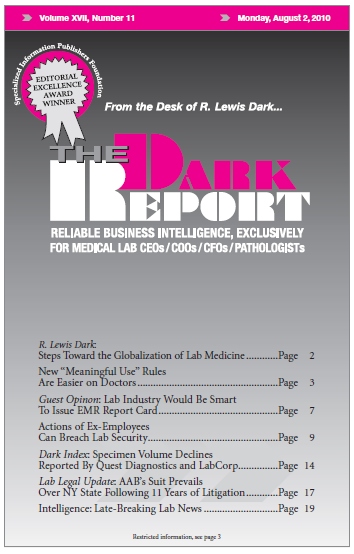
To access this post, you must purchase The Dark Report.