IT WAS NATIONAL NEWS RECENTLY when Quest Diagnostics Incorporated disclosed a security breach involving the protected health information (PHI) of 34,000 individual customers. This episode is a reminder to clinical labs and pathology groups of the need to guard protected health information. In fact, as part of its compliance with federal law, it was Quest …
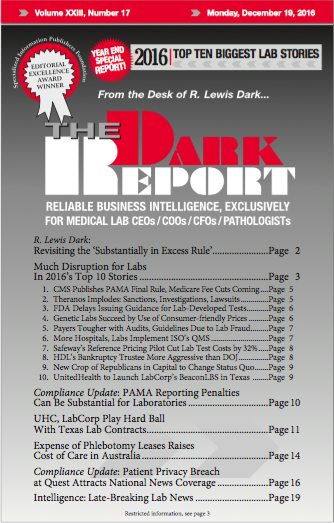
Patient Privacy Breach at Quest Attracts National News Coverage Read More »
To access this post, you must purchase The Dark Report.